Project update 3 of 10
Now online: Serial number verification service
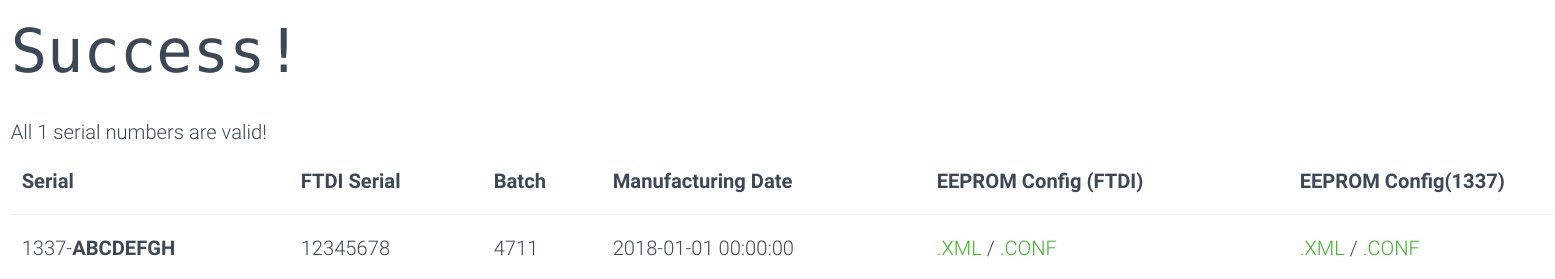
As the first early bird shipments went out today, the online service to verify your devices authenticity has also gone live. Fully functional, but a work in progress.
Using this service you can verify that the device you will receive actually was made by 13-37.org electronics. If you don’t like to use the reCAPTCHA, send me your serial via (PGP encrypted) email, including your public key if you want an encrypted answer.
If you spot bugs or have ideas for improvements or concerns, please let me know!
First 25 early-bird orders shipped!
If you’re one of the first 25 early-birds backers: these don’t have the (just unlocked) imprinted security labels yet.
Honestly, I did not expect the 5000$ goal this fast and am quite busy preparing everything for it to happen in time.
You will receive a hand-signed packing note instead. And it doesn’t really matter if your device has the security label as the serial number is also stored on the USB chip. But it adds another layer of tamper-proofness and an easy way to verify your device is genuine.
I want to look inside!
You can remove the label to take a look inside, as its just an additional layer for proof of authenticity - Warranty is NOT void - but be careful with the enclosure and USB connector when opening it! I have to admit there are cleaner ways to open the enclosure as seen in the campaign - especially with some practice.
Even if there is no known attack vector in which tampering of the hardware would remain undetected by the driver, I still recommend applying a new (custom) label to regain some tamper-proofness.
How can it have a serial number at all?
The USB chip has no reprogrammable logic, but still offers us access to an EEPROM to save application or USB specific data like the Vendor- and Product-ID’s as well as an usually factory programmed serial number (i.e. DM00WOEF)
In the first place, I did not want to change the EEPROM settings at all and just use the "unique" serial numbers from FTDI. But as we’ve been getting close to the 5000$ goal so fast, I continued working on the workflow to create the labels.
It turned out to be very complicated to read-out the actual serial number and print (super-small) labels one by one. And I wasn’t so sure about the uniqueness of FTDI’s serial numbers. Thats why a new serial number is assigned from a database of pregenerated ones right after the final production test has passed. The dataset of the specific serial number is completed with the test results, a batch number, the "unique" FTDI serial and a timestamp.
By integrating this into the automated workflow of device testing I just need to put the right label onto the device (and my script tells me which one goes where).
Can I restore the original serial?
Yes you can! Using the FTDI FT_Prog utility for Windows this is pretty easy. There is also a command line tool ftdi_eeprom included in the fully open-source FTDI driver that I’m using in the production workflow - buts its very low-level.
If you have removed the security label (or did not have one), write down your original serial number before you continue, otherwise you might loose it forever. There is no way for me to associate the serial numbers to purchases, so I won’t be able to help you. Warranty claims are of course still possible, as long as you have the invoice/order receipt - or just something.
Make it an look like the FT240
For a more stealth operation you may want it to look like a default FTDI FT240 USB FIFO device.
You can revert all changes made during the final production test. These are:
| USB Vendor-ID | USB Product-ID | Manufacturer | Description | length of serial number | |
|---|---|---|---|---|---|
| original | 0x0403 | 0x6015 | FTDI | FT240 USB FIFO | 8 chars |
| post-production | 0x0403 | 0x6015 | 13-37.org | Infinite Noise TRNG | 13 chars |
Generated configuration files for both configurations can be downloaded using the verification tool.
Safe - using Windows
Grab the XML file to restore the EEPROM with your devices default identifiers and serial and flash it using FT_Prog.
Safe - using Linux
To get started with the command line tool, you can also download a cleartext config file for use with ftdi_eeprom. Its also pre-filled with the original values from FTDI. Or start from scratch using the provided example.
Flashing it:
./ftdi_eeprom --device d:0x0403:6015:<CURRENT_SERIAL> --flash-eeprom infnoise-ftdi.conf
Unsafe
You can also receive your device’s original serial number through the online verification tool and use FT_Prog or ftdi_eeprom manually. FT_Prog is not fully open source and you can make mistakes by doing manual edits. Not recommended!
Here are some example templates using defaults:
Customize it!
You can change all strings of the USB descriptor and the driver will still recognize it. Just don’t do it too often, as the EEPROM has limited write cycles. Also keep in mind it has only 256 bytes in total.
The USB Vendor- and Product-IDs from FTDI have not been changed by me and I can’t recommend doing so, unless you really know what you’re doing. Warranty may be void and the device may be rendered useless!
EEPROM hexdump
This is what the EEPROM content looks like:
00000000 80 00 03 04 15 60 00 10 80 05 08 00 00 00 a0 14 |.....`..........|
00000010 b4 28 dc 14 00 00 00 00 00 00 09 02 01 05 00 00 |.(..............|
00000020 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
*
00000080 3c 36 c3 c9 01 00 54 9a af 68 30 00 00 00 00 00 |<6....T..h0.....|
00000090 00 00 00 01 44 4d 50 56 39 36 39 35 00 00 00 00 |....DMPV9695....|
000000a0 14 03 31 00 33 00 2d 00 33 00 37 00 2e 00 6f 00 |..1.3.-.3.7...o.|
000000b0 72 00 67 00 28 03 49 00 6e 00 66 00 69 00 6e 00 |r.g.(.I.n.f.i.n.|
000000c0 69 00 74 00 65 00 20 00 4e 00 6f 00 69 00 73 00 |i.t.e. .N.o.i.s.|
000000d0 65 00 20 00 54 00 52 00 4e 00 47 00 14 03 31 00 |e. .T.R.N.G...1.|
000000e0 33 00 33 00 37 00 2d 00 30 00 30 00 30 00 31 00 |3.3.7.-.0.0.0.1.|
000000f0 02 03 00 00 00 00 00 00 00 00 00 00 00 00 ab d3 |................|
00000100