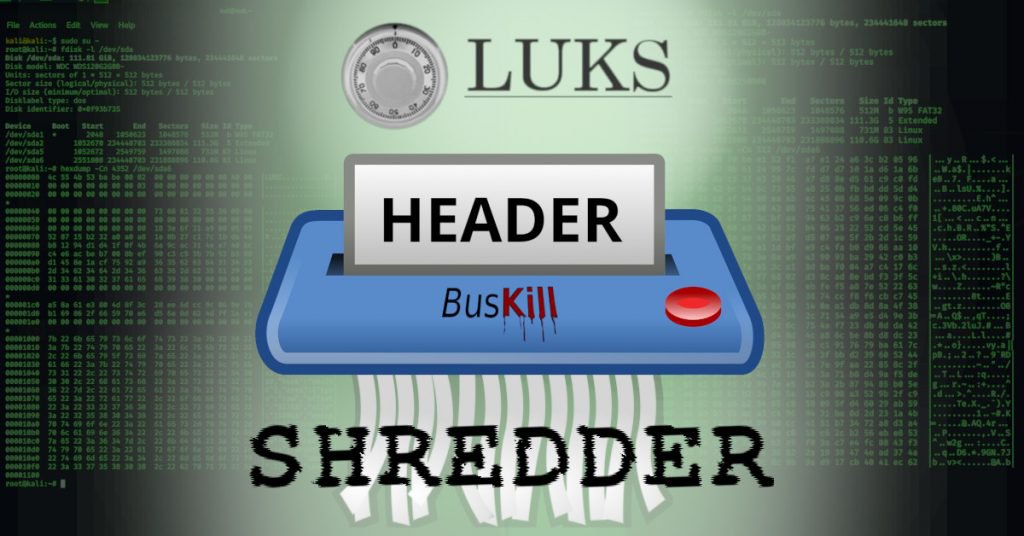
In this update, we present the LUKS Header Shredder — an advanced self-destruct trigger that wipes your full-disk encryption (FDE) master private keys in about 5.2 seconds.
We’ve recieved a lot of questions about the BusKill self-destruct trigger. First, let’s clear-up some confusion:
- BusKill is not designed to harm your hardware. "Self-destruct" means destroying your encrypted data in software.
- BusKill does not and will never ship with "destructive" triggers. Currently, the app only supports the "lock your screen" trigger. Soon we will add a "shutdown" trigger. To prevent the risk of accidental data loss, will will never add self-destruct triggers by default.
- Users will eventually be able to select arbitrary scripts as auxiliary triggers.
- Linux users can now define a self-destruct trigger with a udev rule. Use it at your own risk!
The LUKS Header Shredder trigger for BusKill permanently and irrevocably destroys the ability to decrypt the contents of your LUKS volume. The procedure [a] locks the screen, [b] unmounts the LUKS volumes, [c] wipes the encryption keys from RAM, [d] wipes the encryption keys from disk, [e] wipes the rest of the FDE header metadata, and [f] does a hard-shutdown.
This whole process completes in just a matter of seconds and renders everything on the LUKS volume indistinguishable from random data. (Our guide provides a forensic evaluation that backs up up this claim.)
To view the source code and get instructions on how to configure your computer to self-destruct when your BusKill cable’s connection is severed, see our LUKS Header Shredder guide, which is hot off the presses!
We still have some Early-Bird discounts available! Get your BusKill cable for $10 off while they last!