New Firmware With Support For Keystroke Reflection, Dynamic Hardware ID Spoofing, OS Detection, and More!
I want to sincerely thank you for your patience and apologize for the delay in releasing our final firmware. I’ve been heads down working on something new: Diabolic Parasite, a next-level red teaming tool that brings extreme stealth and covert capabilities. Meanwhile, the final Diabolic Drive firmware is here, and it’s worth every moment of development time! This firmware revision unlocks game-changing capabilities... Read the full update.
Alternate Data Streams (ADS) for Covert Payload Delivery & Data Exfiltration
Greetings everyone! In today's update, I will show you how you can utilize Diabolic Drive's flash storage to deliver your payload or exfiltrate data from a client's target system using Alternative Data Streams (ADS). Read the full update.
Manufactured, Fully Tested, and Shipping Soon!
Hi everyone, Today I'm very glad to inform you that the Diabolic Drive orders were all manufactured, fully tested and packaged. They have been shipped to Mouser and very soon to your homes. Read the full update.
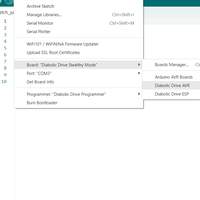
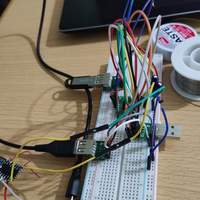
Introducing the Diabolic Drive ISP Programmer
We've made a very simple ISP programmer with USB TYPE-C to interact with the Atmega32u4 bootloader on the Diabolic Drive. Read the full update.
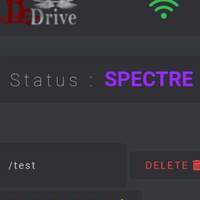
Introducing Spectre, Our Latest Stealth Feature
Spectre takes Diabolic Drive's wireless keystroke-injection mechanism to a whole new level. Previously, when connected to a computer, Diabolic Drive would present simultaneously as an HID interface and as a 64-GB flash drive. This design was already cutting edge, in terms of evading detection, because a flash drive is precisely what one would expect to see when plugging in a device like this. But now, rather than entering the "active" state immediately when inserted, Diabolic Drive defaults to the "spectre" state, which presents only as a flash drive...right up until you deem it safe to expose the HID interface and begin injecting keystrokes, at which point you can initiate the attack remotely over a Wi-Fi connection! Until then, the HID interface will remain completely dormant, with no unexpected behavior to detect and no abnormal logs generated. And Spectre is compatible with Diabolic Drive's other stealth features, as well, so you can still hide the Arduino bootloader, spoof VIDs and PIDs, etc. This update includes a proof-of-concept video demonstration that shows Spectre in action! Read the full update.
Extending the Campaign, Reducing Funding Goal, and Introducing a New Stealthy Feature!
We've made some changes to the campaign, with exciting updates coming soon. Read the full update.
Diabolic Drive USB Type-C support
This will be a quick update about USB Type-C support for the Diabolic Drive. Read the full update.
Utilizing Diabolic Drive as a Powerful 4.1 dBi Wi-Fi Deauther
Check out the ways you can use Diabolic Drive as a Wi-Fi deauthentication attack tool Read the full update.
Diabolic Drive Supported Enclosures
Learn about all the enclosures that work with Diabolic Drive Read the full update.
Price Cut, Product Inspiration, and What Makes This One Special
Learn about how the Diabolic Drive works and what makes it so unique Read the full update.
Our Campaign is Now Live on Crowd Supply!
Diabolic Drive is a stealthy, modern, wireless keystroke injection tool in a universal flash drive PCB form factor with 64 GB storage Read the full update.