Nth Dimension
Security & Privacy
PCBWay
Nth Dimension
Security & Privacy
PCBWay
Signet HC is a secure USB drive, and the successor to our first product, Signet. It’s built with open-hardware and free and open source software. In addition to being an encrypted flash drive, it is also a two-factor authentication (2FA) device and a hardware password and personal information manager, making it a portable solution to a variety of data security problems. Signet HC’s encrypted data is password protected and can be unlocked through its cross-platform client application (available on Windows, MacOS, GNU/Linux, and Android). For convenience, the client software is stored on the device in a read-only partition allowing you to use it without downloading software.
Signet is physically secured in the sense that a user must take physical action (press a button on the device) to allow sensitive commands to be executed. Physical security blocks any malicious software from executing commands on the device. Signet HC’s physical security features make it resistant to malware in a variety of environments. Signet implements physical security by requiring the user to press its button to permit the execution of any sensitive command; the button flashes blue when any sensitive command is sent to the device.
Two-factor authentication requires the presence of a secure device in order to log in to a website or complete an important transaction. Two-factor authentication compensates for weak or compromised passwords. Signet HC implements the FIDO U2F and FIDO2 two-factor authentication protocols used by a variety of popular websites. Once you have paired Signet HC with a compatible website, you can complete your log in or transaction by pressing the device button when its light flashes. For added security, Signet HC can be configured to disable two-factor authentication features until the device is unlocked.
Signet HC can contain several types of storage volumes in its embedded 32 GB flash memory, each suited to different purposes:
Signet HC implements the password management features we developed in the original Signet device: it stores a password database in an encrypted format inside its microcontroller’s internal flash memory. Once the device is unlocked you may view the data directly in the client and copy to the clipboard.
The client supports browser plugins for Firefox and Chrome that can fill in data such as login and password information on text forms. The client can also forward the data to the device’s USB keyboard interface to type data directly into another application. For website logins, the keyboard device will enter <tab> and <enter> keystrokes to log in to the website with a single request.
Signet HC is not limited to storing information about account passwords. Instead, it has a flexible database structure that allows you to create new data types and to add fields to individual entries for notes and associated data. This allows you to safely store any data you data you wish to keep off the cloud.
Keeping your Signet HC with you comes with the risk of losing the device. You can configure Signet to regularly back up your data when connected to your primary computer, to either your computer’s hard disk or a designated removable media device such as a USB stick or memory card. The Signet client can then read the backups when you provide the master password, giving you immediate access to your data and the option to upload the data to a replacement device. Since backing up the storage volumes can be time consuming their backup options can be done with a different policy or backup frequency.
Signet HC will support the storage and generation of asymmetric cryptographic keys. In addition to storing such keys, Signet HC can perform actions with them such as file encryption, file signing, and SSH authentication. With Signet HC, you can securely use your private cryptographic keys in any environment.
Our aim is to support most of the common functions of the GNU Privacy Guard (GPG) software suite. There is such a wide variety of cryptographic algorithms in use that there are likely to be some algorithms we wont support immediately. However, it should be easy to add new cryptographic algorithms over time. We will listen to our users to determine which features are most important.
Signet HC supports the creation of multiple profiles, each with its own unlock password. Each profile can be configured to display only some database entries or storage volumes stored on the device. This allows you to create different profiles with different settings to prevent sensitive information being seen by eavesdroppers. A common use case would be keep your personal accounts (such as dating sites, online shopping, etc.) invisible when you’re at work. The multi-profile feature provides "plausible deniability" since it is not possible to know about the existence of the different profiles without knowing their unlock passwords. Signet HC makes it easy to maintain multiple profiles by allowing you to assign tags to data. When you create a profile you can specify a set of tags that will be visible in that profile.
As with the original Signet, we will release source code and CAD files for Signet HC before we deliver the devices. We will release the software under the GPLv3 license and the hardware specifications under the CERN Open Hardware License v1.2. We believe sharing our files under free software licenses is essential to developing a credible, secure system — closed systems can harbor defects or even backdoors that are harder to find and fix compared to open systems. We invite outside observers to study our systems to look for any security flaws.
Our devices will not be locked down by default, allowing you to upload your own firmware. Users are free to study the design, make changes to the hardware or firmware as they see fit, or even develop entirely new applications for the hardware.
You’ll be able to choose to lock down the firmware to add a level of tamper resistance to the device. Even locking down the firmware is reversible as long as the device data is wiped first. This increases the difficulty of attacking a stolen device while still protecting a user’s right to use the device for another purpose after locking it down.
In order to make the hardware itself expandable, we have exposed several electrical signals on the board:
Signet HC offers a number of new hardware and software features compared to Signet. Signet contained only a 256 KB microcontroller flash memory whereas Signet has a 32 GB eMMC memory in addition to a 512 KB microcontroller flash memory. It is also runs substantially faster at 216 Mhz with a cryptographic accelerator. The original Signet ran at only 48 Mhz with no cryptographic accelleration. Signet’s capabilities were well suited for managing and encrypting its personal information database. Signet HC’s more advanced capabilities allow it keep Signet’s database capabilites, handle mass storage encryption and perform many other new fuctions.
| Signet HC | Iron Key D250 | Kingston Vault privacy | Nitrokey Storage 2 | |
|---|---|---|---|---|
| Length | 52 mm | 75 mm | 78 mm | 70 mm |
| FIDO U2F support | Yes | No | No | No |
| One-time password (OTP) support | Yes | No | No | Yes |
| Password management features | Yes | No | No | Limited |
| Private key storage/algorithms | Yes | No | No | Yes |
| Physical Security Features | Yes | No | No | No |
| Encrypted read/write speed (averaged) | 15 MB/s | 19 MB/s | 66 MB/s | 5.5 MB/s |
| Mass storage capacity | 32 GB | 16 GB | 32 GB | 32 GB |
| Price | $80 | $268 | $100 | $182 |
There’s a wide range of prices for encrypted storage devices, but we think most are priced much higher than they should be. Unfortunately, we cannot exceed the transfer speeds of the proprietary USB storage drives we have looked at. Notably these products generally don’t offer significant features beyond drive encryption. Another factor is that we have prioritized keeping Signet HC compact. All devices offering encrypted mass storage capabilities we’ve looked at are 70mm or longer. We limited our device length to 52mm which is the length of the average house key.
The Signet HC device has three parts: printed circuit board assembly (PCBA), button, and enclosure.
Assembly consists of inserting the button and PCBA into the enclosure halves and snapping the enclosure halves together. After assembly, each unit will go through a basic functional test and have its eMMC memory tested for bad blocks. Devices that pass the functional test and two rounds of bad block checking will be deemed suitable for shipping.
We will ship assembled Signet HC units to Crowd Supply for distribution to backers. For more information, see Crowd Supply’s ordering and shipping page.
We have reduced many campaign risks by building production-quality prototypes and putting them through stress tests as well as everyday use cases. The main remaining risks we see are:
We will have our volume PCBA orders manufactured by PCBWay, which is a different company than the one we used to build our prototypes. They are a reputable company but there is always a risk that miscommunication or differences in their manufacturing processes will reveal new problems. By limiting the size of our initial production order, we will be giving ourselves a chance to correct any initial issues before they become too costly.
Both our microcontroller and eMMC memory chip of choice are not well stocked by distributors. We have procured 250 eMMC chips in advance to make sure there are no delays in our initial order of 100 PCBAs. It’s possible that at higher volumes fulfillment could be delayed while we locate new suppliers or wait for distributors to refresh their stock.
We are promising many software features, some of which are not present in the original Signet and have not been prototyped yet for Signet HC. In many cases, there are open source projects and libraries that we can incorporate or refer to, so these features can be added rapidly. That said, there is still a risk that fulfillment gets delayed by software development alone. In this case, we may decide to ship the hardware with some software features missing and then provide the missing features in an update.
"Anyone who needs to carry (and share) sensitive information needs to look at this device."
"The latest version of the Signet thumbdrive is the Signet HC. The HC has a number of enhanced features and a lower price point, making it an attractive alternative to other high-security flash drives."
"[Translated] The Signet HC of Nth Dimension is a USB key designed for use in the field of security. It allows its users to have a two-factor authentication while keeping their passwords completely secure."
"Signet blocks any malicious software from executing commands on the device."
Produced by Nth Dimension in Fremont, CA.
Sold and shipped by Crowd Supply.

Helps keep your Signet HC close to your keyboard when the closest USB port is too far away. Can also reduce strain on the device's connector to increase its lifespan. 3'

An all-in-one physically secured USB flash drive, authentication tool, and personal information manager you can take with you wherever you go.

Connects your Signet HC to a USB-micro Android device. 6"

Connects your Signet HC to a USB-C Android device. 6"
An open-source, manual pick-and-place machine for PCB artisans
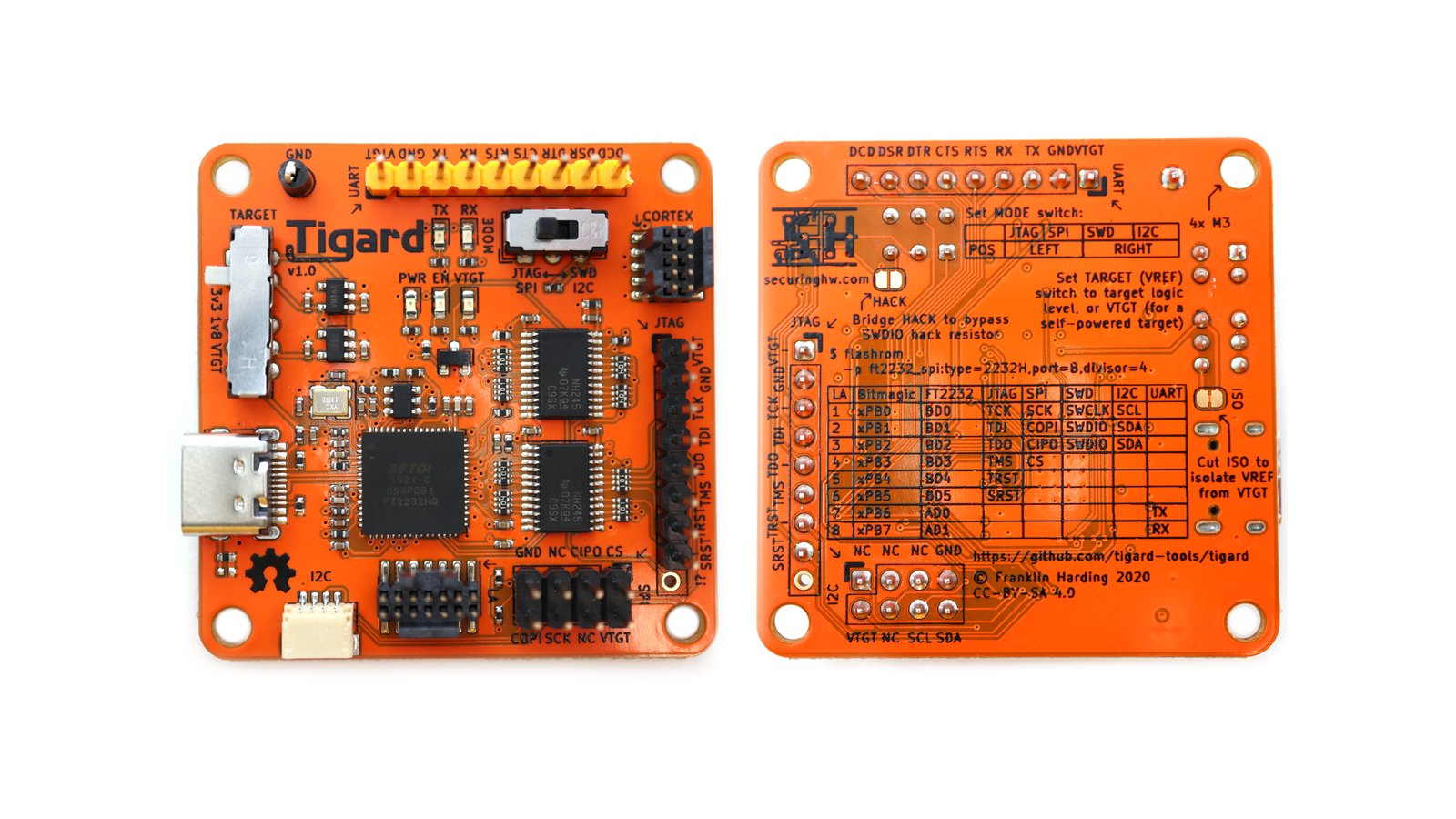
An open source FT2232H-based, multi-protocol, multi-voltage tool for hardware hacking
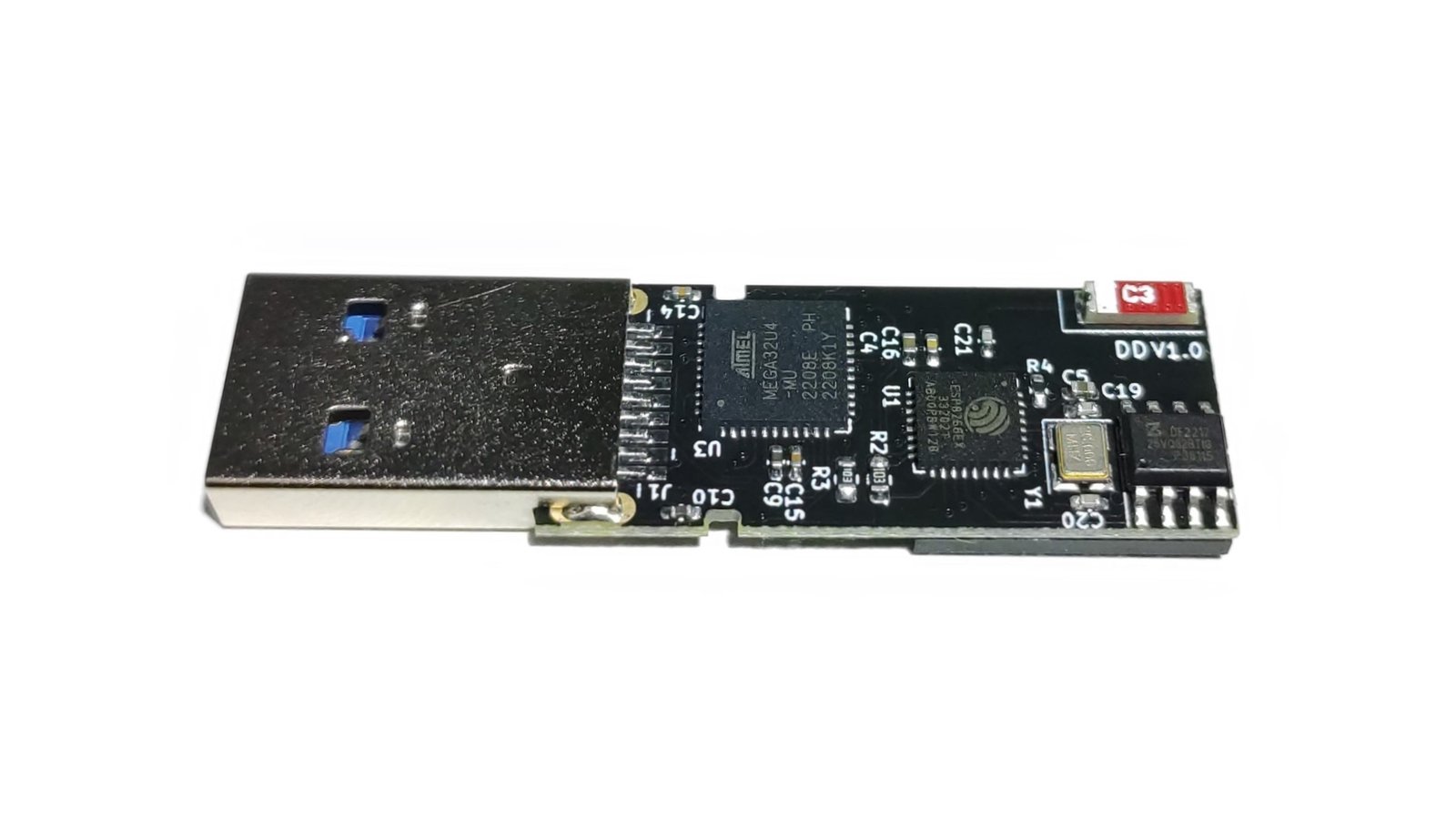
Stealthy, modern, wireless keystroke-injection tool in a universal, four-layer, double-sided flash-drive PCB form factor with 64 GB of storage