Security & Privacy

KrakenSDR
A phase-coherent software-defined radio with five RTL-SDRs
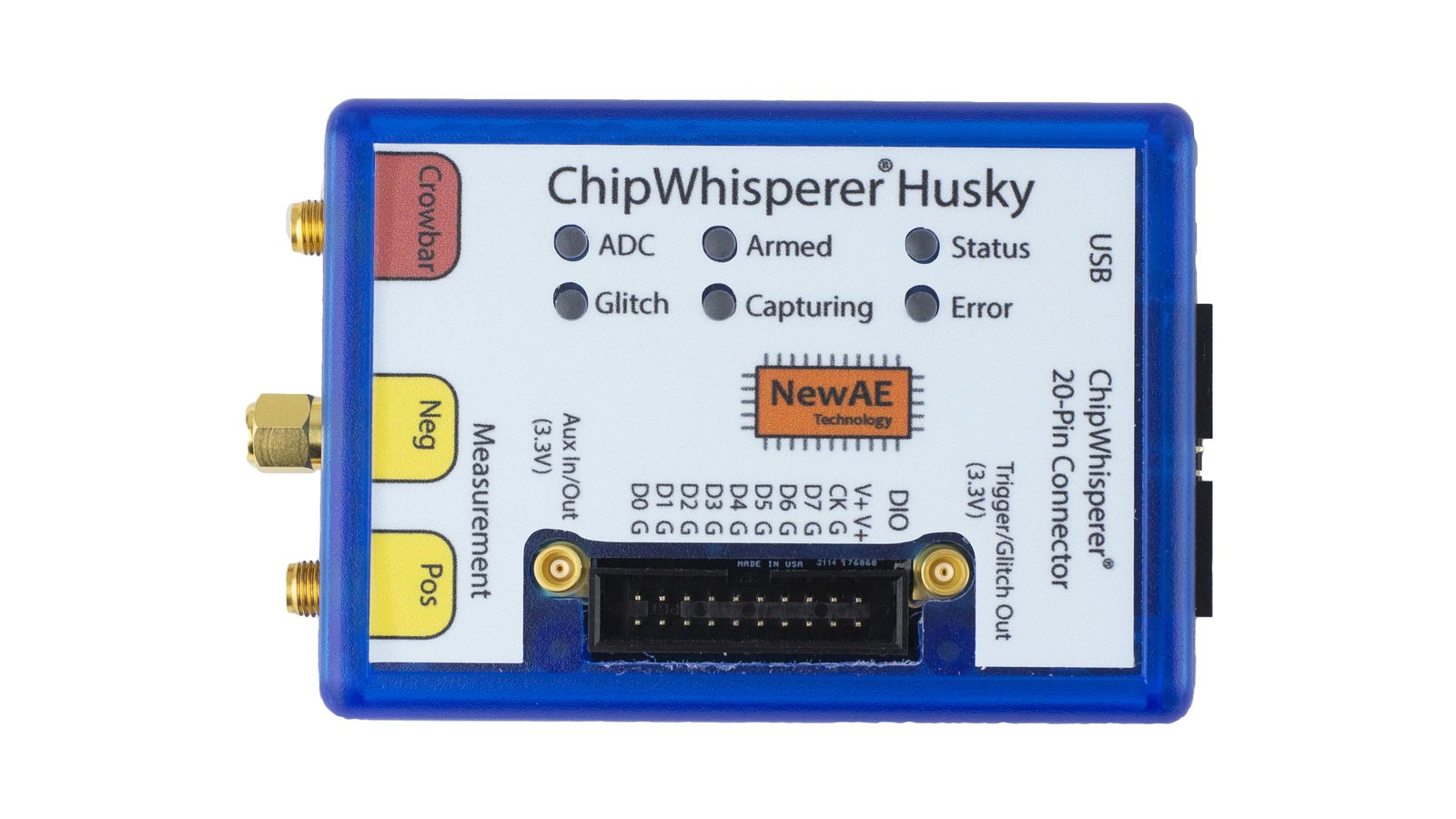
ChipWhisperer-Husky
The power-analysis and fault-injection tool you can hold in your paw

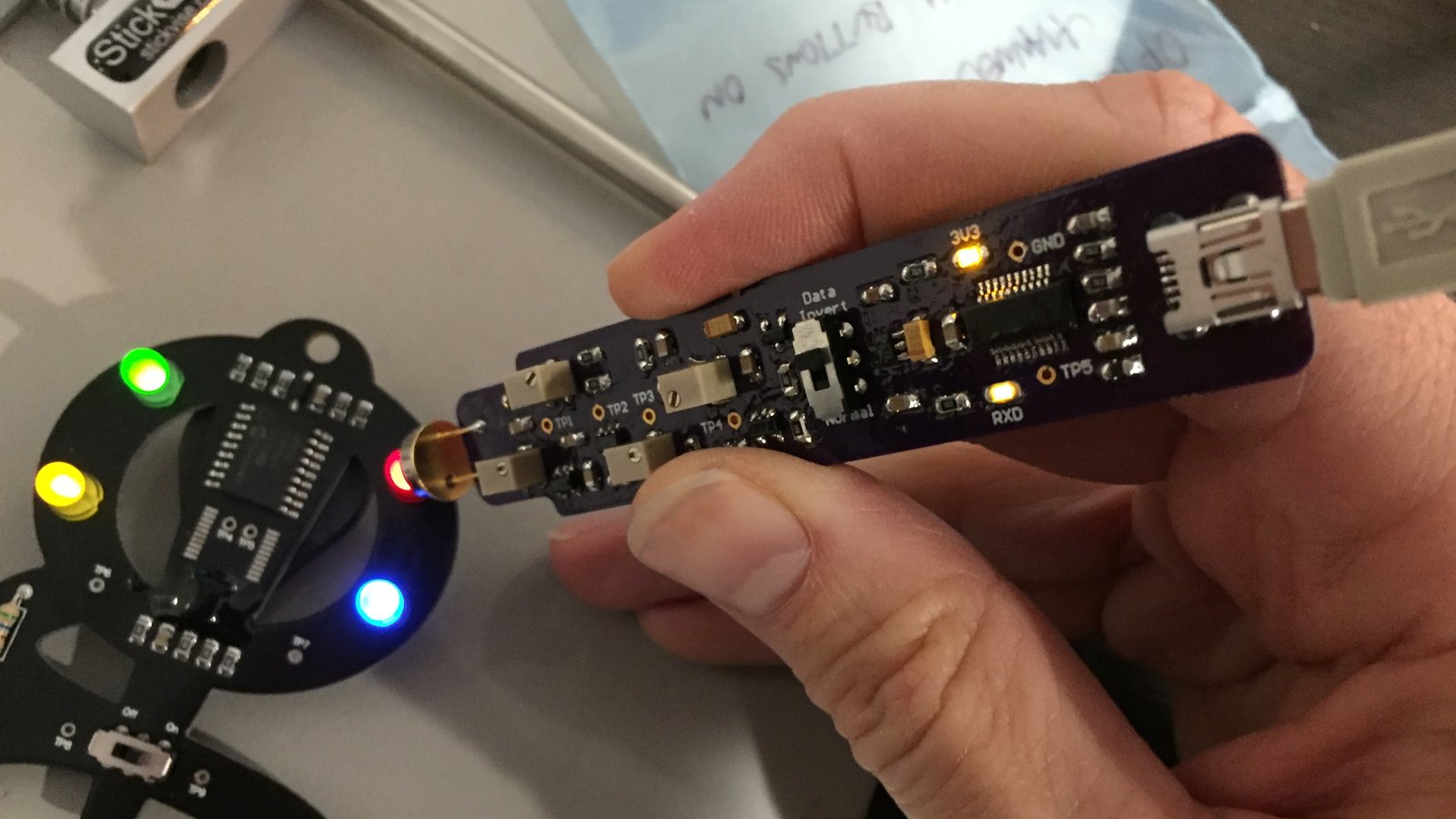
Cynthion
A multi-tool for building, analyzing, and hacking USB devices
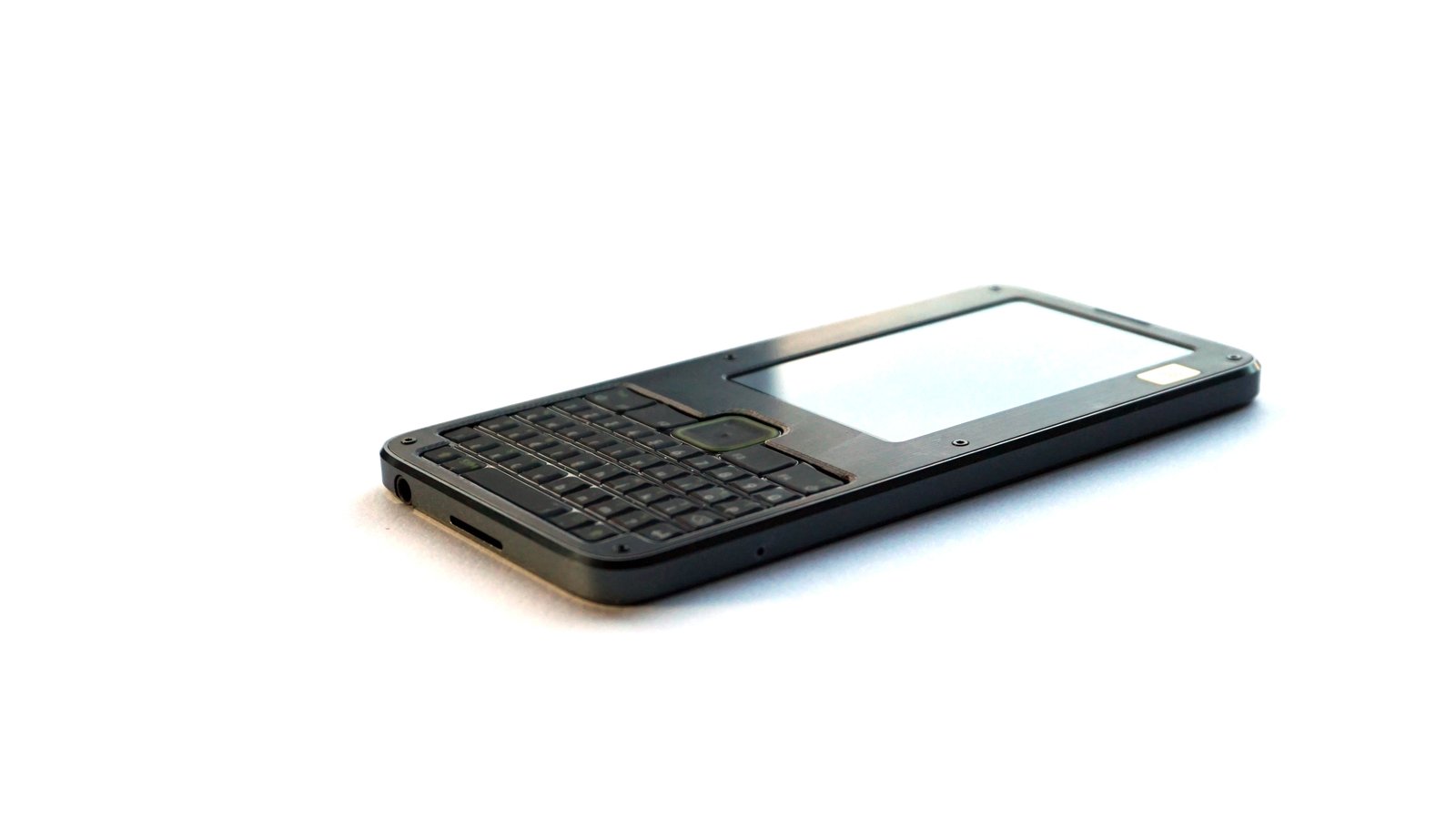
Precursor
Mobile, Open Hardware, RISC-V System-on-Chip (SoC) Development Kit
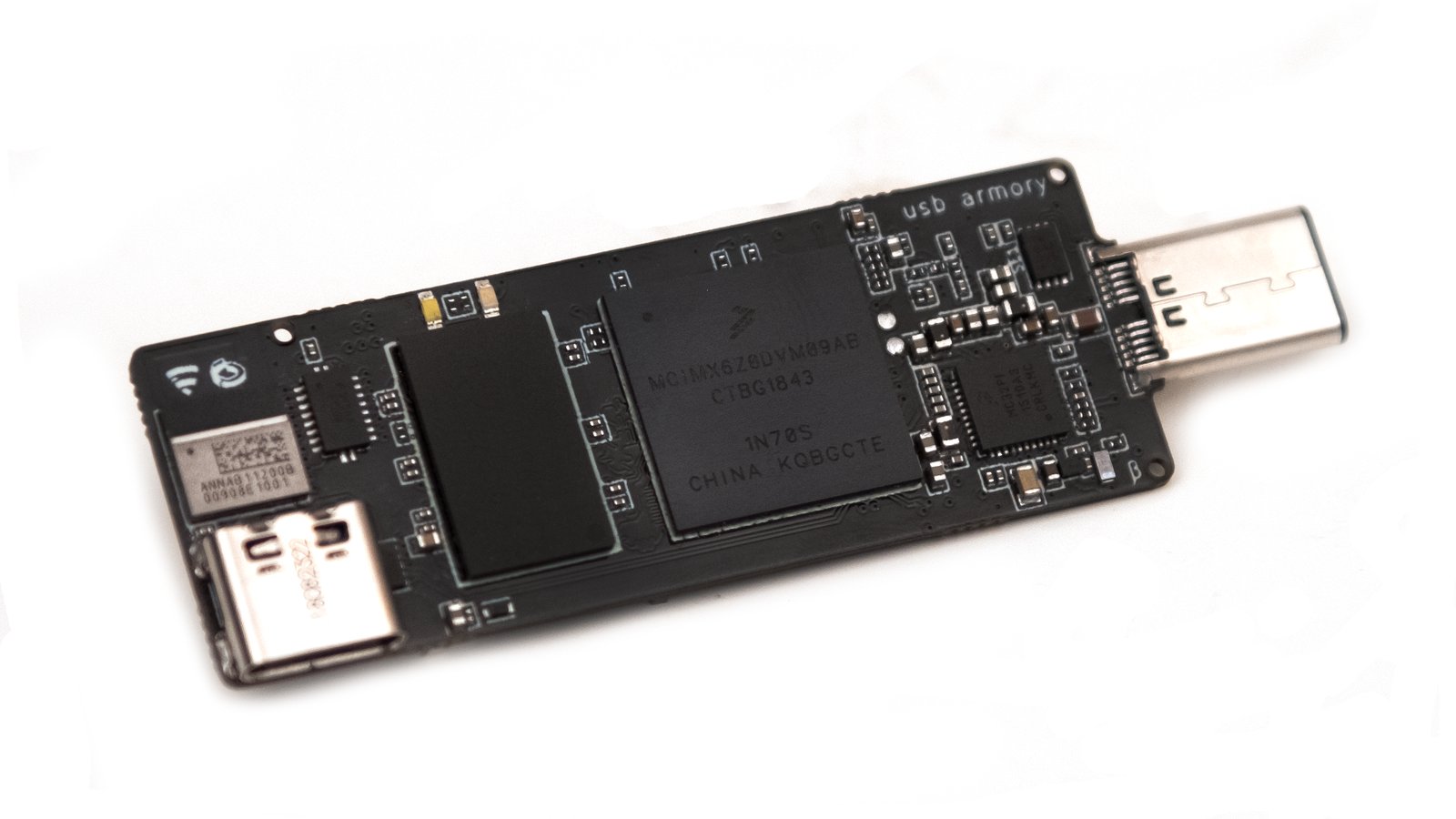
USB armory Mk II
A tiny, open source USB computer for security applications

Somu
A tiny FIDO2 security key for two-factor authentication and passwordless login

Infinite Noise TRNG
Open hardware USB true random number generator
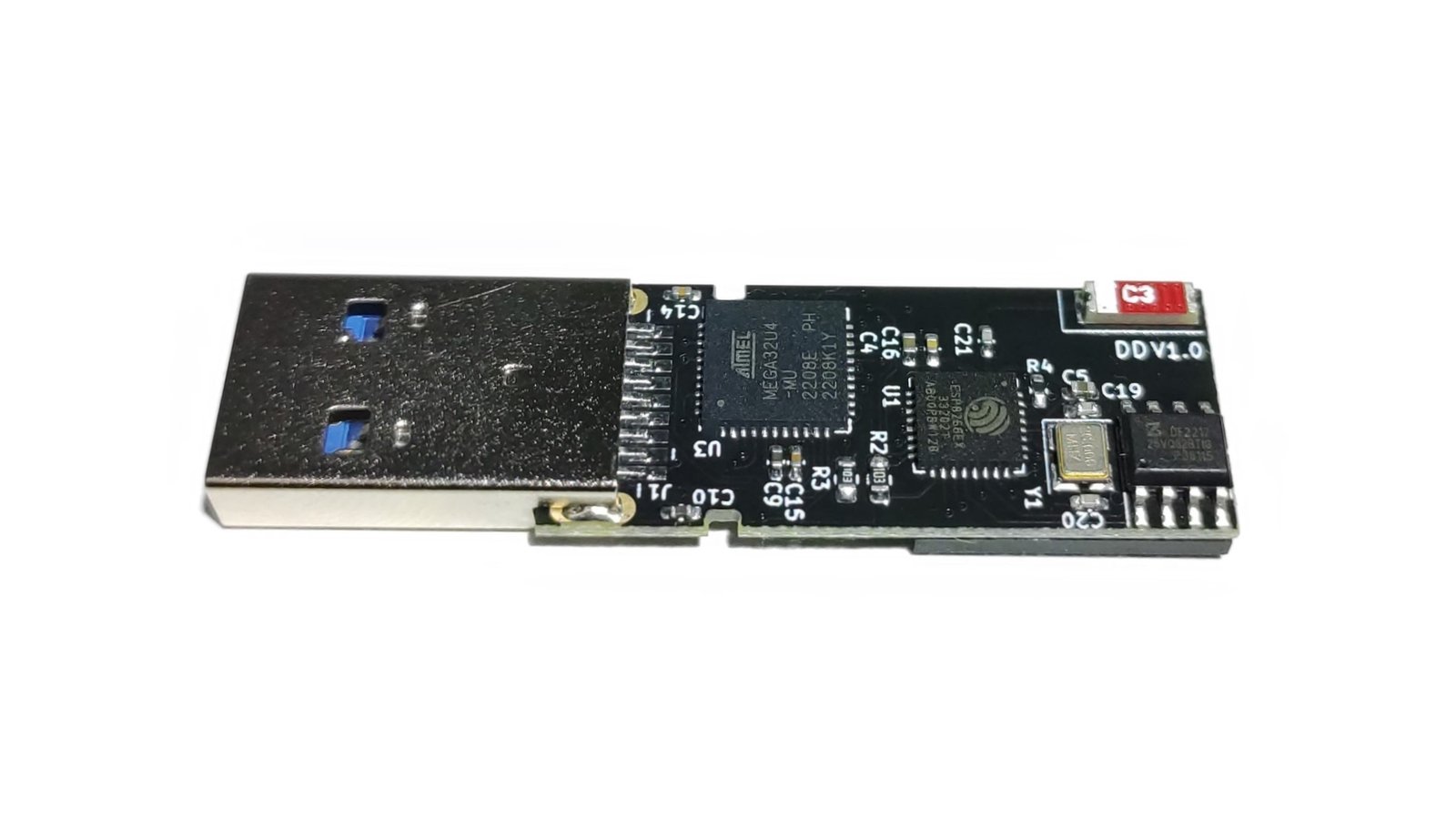
Diabolic Drive
Stealthy, modern, wireless keystroke-injection tool in a universal, four-layer, double-sided flash-drive PCB form factor with 64 GB of storage

DiceKeys
Security keys you create by rolling dice
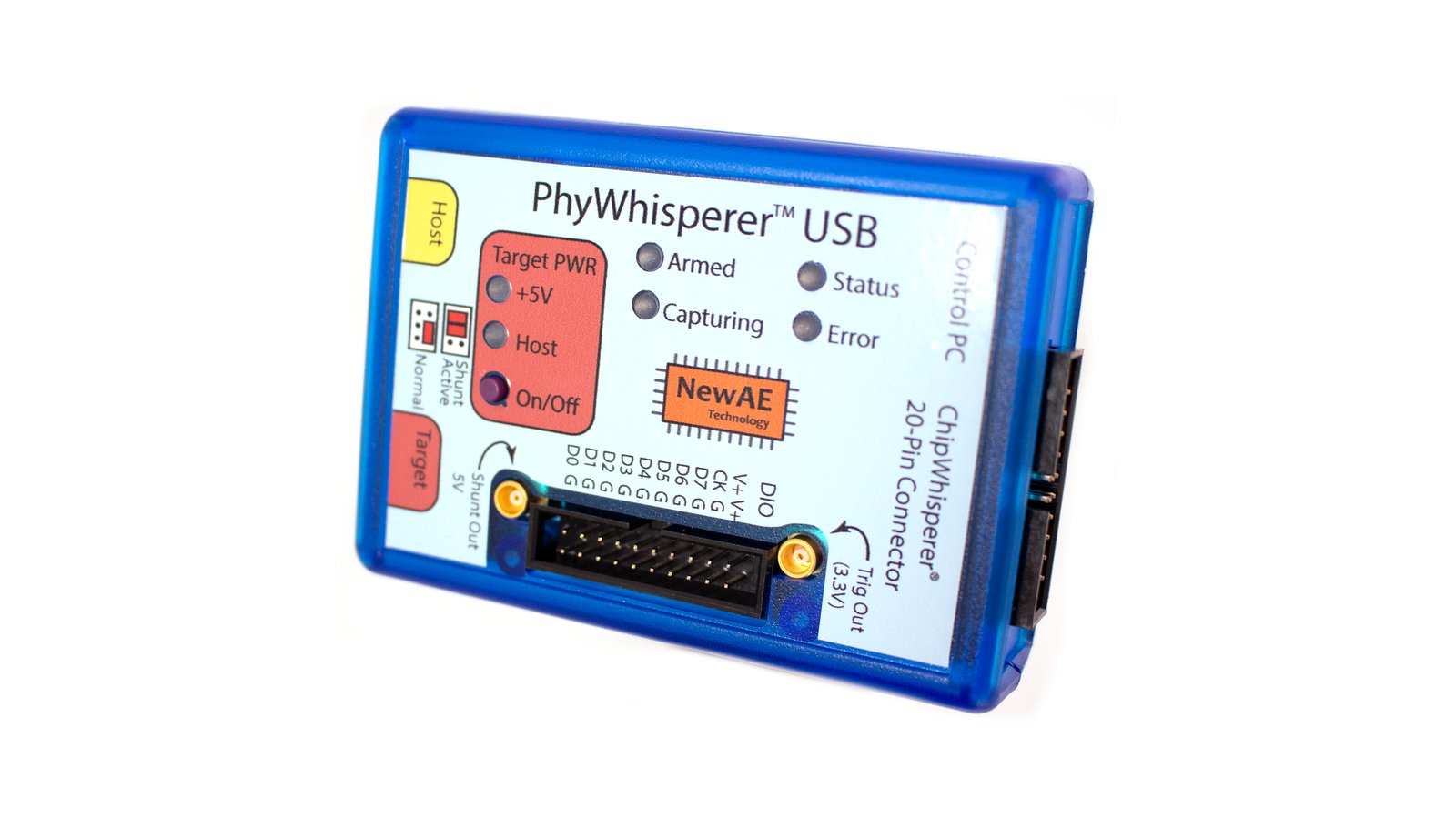
PhyWhisperer-USB
A hardware-based USB 2.0 monitor & trigger platform, controlled from Python

ProxmarkPro
A handheld RFID & NFC test instrument optimized for untethered use in the field

The Skull CTF
A mind-bending hardware puzzle in three acts

AI in a Box
Your own offline, private, open source LLM for conversations and more

Ovrdrive USB
A privacy-focused, open-hardware USB flash drive with a hidden feature that protects your data
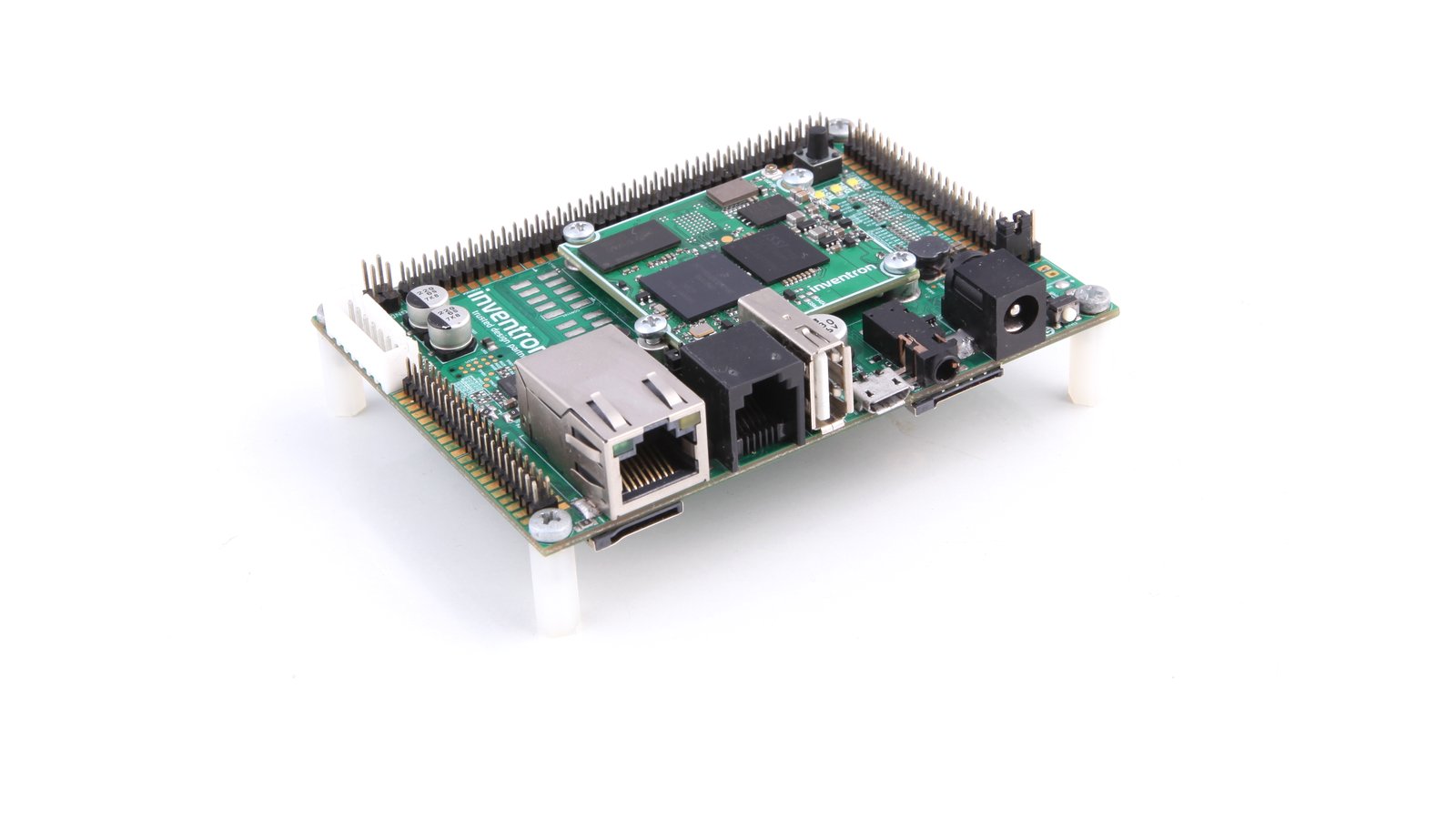
Invensom 6UL SoM & SBC
A secure, high-performance, ARM-based system on module & single board computer with support for Wi-Fi & Bluetooth connectivity

unsurv offline
An open source, privacy friendly, compact GNSS receiver with ESP32 and NFC for all your location based projects, including tracking surveillance cameras

BusKill
A USB kill cord for your laptop
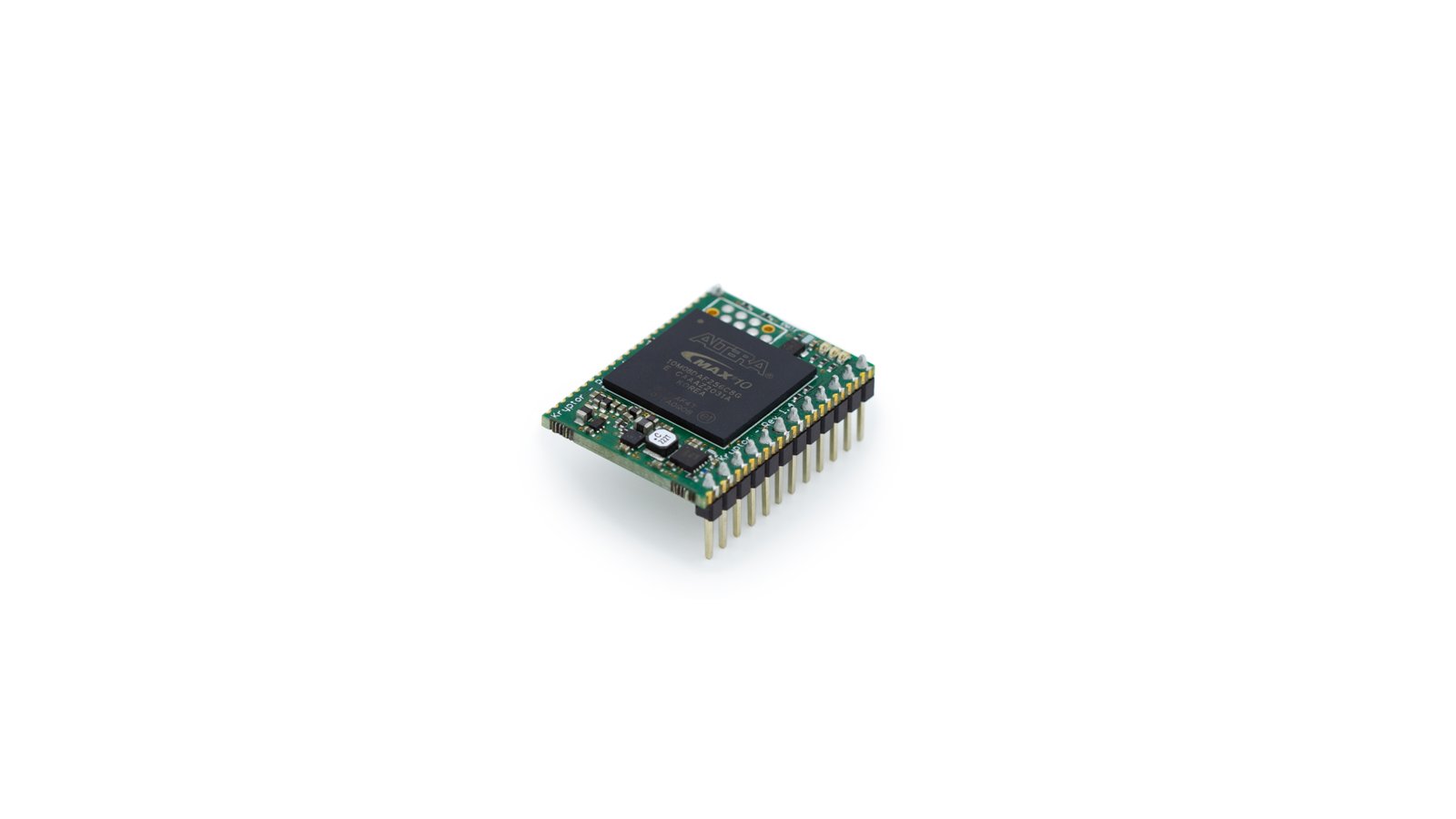
Kryptor FPGA
A one-chip hardware security module (HSM) and MAX10 FPGA dev board

Signet High-capacity
An all-in-one encrypted USB flash drive, two-factor authentication token, and password manager

USBNinja
BadUSB embedded into a USB cable
OpticSpy
A tool to explore optical data transmissions and covert channels

Pastilda
Open source hardware password manager

UsbSafe²
An open, programmable dongle for protecting USB devices from USB hosts and chargers.

Librem 13 Laptop
The first high-end laptop that respects your privacy, security, and freedom

Librem 15 Laptop
The first high-end laptop that respects your freedom and privacy

USB armory
An open source USB stick computer for security applications.

Signet
Physical security for your personal data
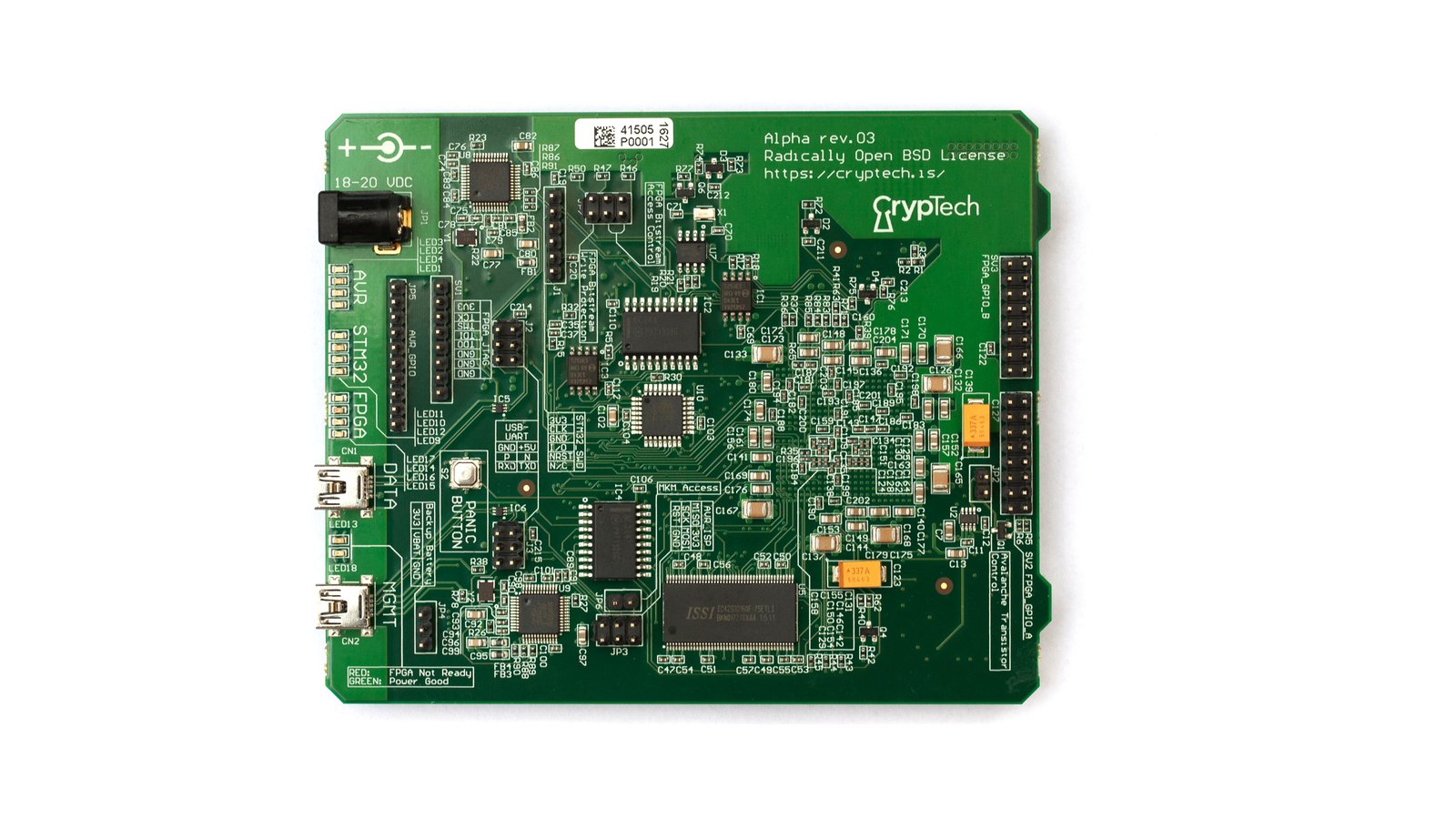
CrypTech Alpha
An independent international development effort founded to create a trusted, open source, inexpensive, hardware cryptographic engine.

ORWL
An open source, physically secure personal computer.

Premium USB Armory Enclosure
Protect your USB Armory Mk I in style with this milled PaperStone and anodized aluminum enclosure.

